📑Table of Contents:
- What is a SIM Swap Anyway?
- Phone Number: A Hacker’s Golden Goose?
- Are There Other Phone Number-Based Hacks?
- So, How Can I Protect Myself?
- Why Hackers Love Mobile Vulnerabilities
- How Big is the Threat, Really?
- Behind the Hacker’s Mind: What Drives Them?
- Hidden Dangers: Less Known Phone-based Hacks
- Mitigating Risks: Becoming Cyber-Savvy
Phones buzz. Messages ding. But lurking beneath these everyday sounds could be a silent threat: SIM swap and phone number-based hacks. Let’s embark on this journey to decode these threats and bolster our defenses!
What is a SIM Swap Anyway?
Let’s paint a picture. You’re enjoying your coffee, scrolling through notifications. Suddenly, silence. No signal. And just like that, your phone number is hijacked! This digital heist? It’s called a SIM swap.
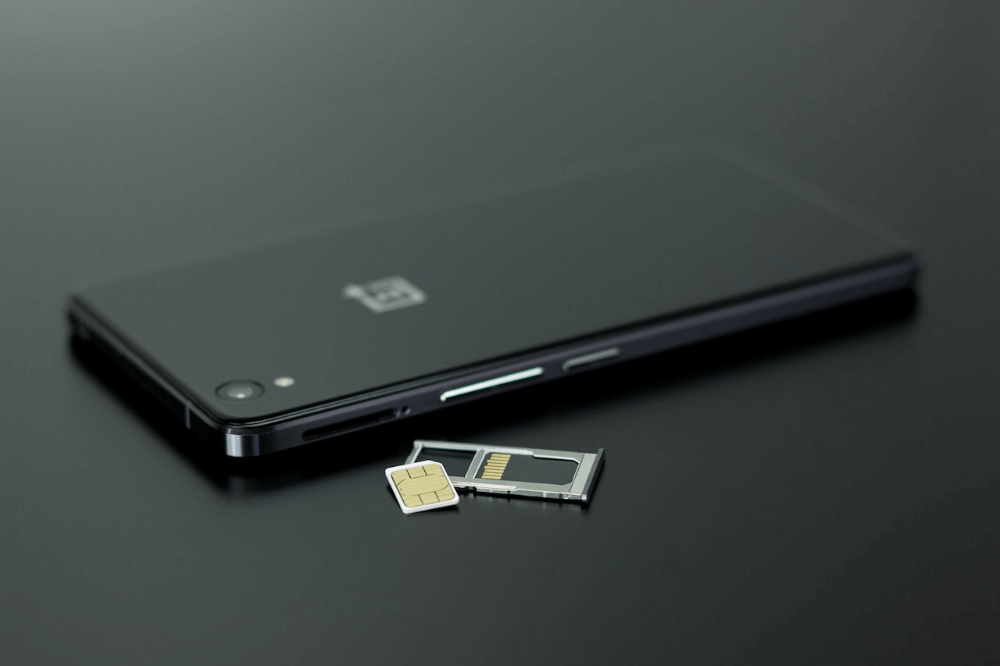
In a SIM swap, hackers finagle control of your phone number. By sweet-talking customer service or exploiting security loopholes, they transfer your number to a new SIM card. And now? They’re impersonating you, intercepting your texts, and potentially accessing your accounts.
Phone Number: A Hacker’s Golden Goose?
Why the fuss about phone numbers? They’re more than just digits. They’re gateways. From bank accounts to email logins, our numbers are tied to critical security protocols, particularly two-factor authentication (2FA). Hackers know this. By capturing your number, they’re one step closer to unlocking your digital treasures.
Are There Other Phone Number-Based Hacks?
SIM swap might be trending, but it’s not the sole villain. There’s a bigger rogues’ gallery:
- Voice phishing (vishing): Are those “official” calls from your bank or a tech giant? They might be fake. The goal? Deceive you into revealing precious data.
- SMS phishing (smishing): Crafty texts with too-good-to-be-true offers or alarming alerts, guiding you to malicious sites.
- Missed-call scams: Mystery calls from foreign numbers hoping you’ll call back, resulting in hefty charges.
So, How Can I Protect Myself?
Now, onto the good stuff. Protection! Here’s your action plan:
- Guard your number: Treat it like gold. Avoid plastering it on public platforms or sharing it indiscriminately.
- Authentication apps to the rescue: Move to app-based 2FA. Platforms like Google Authenticator or Authy are safer bets than text-based codes. While trying to protect yourself from sim swaps and other phone number-based hacks, learn how to protect your password.
- Educate and update: Stay informed about the latest scams. Regularly update your phone’s software for added security patches.
- Provider partnership: Collaborate with your service provider. Set up extra security layers, like unique PINs or passwords, for account changes.
Why Hackers Love Mobile Vulnerabilities
Mobile phones have evolved from mere communication tools to indispensable life companions. For many of us, they’re virtual wallets, photo albums, and even workstations. But here’s the kicker: as our reliance on them grows, so does their appeal to cyber criminals.
How Big is the Threat, Really?
You might think, “This won’t happen to me.” Think again. Statistics paint a different picture. Reports show a consistent rise in phone-based cyberattacks. With the expanding digital landscape, hackers are finding richer hunting grounds. Your phone isn’t just at risk; it’s a prime target.
Behind the Hacker’s Mind: What Drives Them?
Curiosity? Profit? Revenge? All of the above. Hackers have varied motivations:
- Financial gains: This one’s obvious. Stealing your bank credentials or accessing financial apps can lead to immediate monetary benefits.
- Data theft: Personal data, when accumulated and analyzed, becomes a goldmine. It can be sold, used for identity theft, or even held for ransom.
- Control and power: For some, the thrill isn’t in the loot but in demonstrating their ability to disrupt and dominate.
Hidden Dangers: Less Known Phone-based Hacks
While SIM swaps and phishing attempts grab headlines, other covert threats lurk:
- Spyware: Silent apps that monitor your activities, capturing everything from key presses to camera access.
- Wi-Fi eavesdropping: Using unsecured Wi-Fi? Hackers could be ‘listening’ to your online activities.
- Camera and microphone hacks: The idea that someone could remotely access these is unsettling, but it’s possible.

Mitigating Risks: Becoming Cyber-Savvy
Protection isn’t just about tools; it’s also about mindset:
- Awareness: Recognize that threats exist. Complacency can be your biggest enemy.
- Regular audits: Check your apps. Why keep something you don’t use, especially if it might have vulnerabilities?
- VPN is your friend: When on public Wi-Fi, use a Virtual Private Network to encrypt your activities.
- Physical safety: A simple screen lock can deter potential threats. Additionally, be mindful of where and how you use your phone, especially in public spaces.
Last Words But Not Least!
Our digital age, while shimmering with conveniences, also casts shadows of threats. SIM swaps and phone number hacks remind us of the lurking dangers.
But with knowledge, vigilance, and proactive measures, we can navigate this minefield securely. Let’s pledge to be aware, share this knowledge, and create a safer digital community for all!





